In today’s digital world, even with the utmost efforts to safeguard data, there remains a risk of losing control, especially when data is transmitted over the internet. To mitigate this risk, one effective method is encryption. By encrypting data, it becomes incomprehensible and unusable to unauthorized parties who lack the means to decrypt it.
Note
Cryptography is a comprehensive and well-covered subject in numerous cybersecurity books. To maintain a focus on the topics of cloud security, this book will only address its crucial and pertinent aspects in the context of cloud environments.
Cryptography is the science and practice of securing information by converting it into a secret code, making it unreadable and unusable to unauthorized parties. It plays a crucial role in ensuring data confidentiality, integrity, authentication, and non-repudiation, making it a fundamental tool for protecting sensitive information and communication in various digital systems, including computer networks, cloud computing, and online transactions.
Encryption
Encryption is a specific process within the field of cryptography. It is the technique of converting plaintext data into ciphertext using cryptographic algorithms and keys. The purpose of encryption is to protect data during transmission or storage by making it unreadable and unintelligible to unauthorized individuals or entities.
Encryption is pure mathematics. There is a defined complex method/formula to encrypt messages and decrypt those messages; you should have the same method or formula to decrypt them. Over time, encryption has achieved complexity due to attackers continuing to find ways to decrypt messages.
There are two different types of encryption: symmetric and asymmetric.
In symmetric encryption, the same secret key is used for both encrypting and decrypting data. This means that both the sender and the receiver need to possess the same secret key to securely communicate and exchange information:
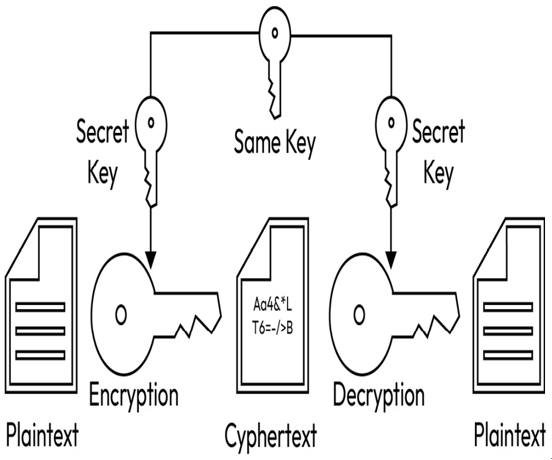
Figure 1.9 – Symmetric encryption (https://binarycoders.files.wordpress.com/2020/07/01_symetric_encryption.png?w=1024)
Asymmetric encryption, also known as public-key encryption, is a cryptographic technique that uses a pair of keys (public key and private key) for secure communication and data exchange. The public key is used for encryption, while the private key is used for decryption:
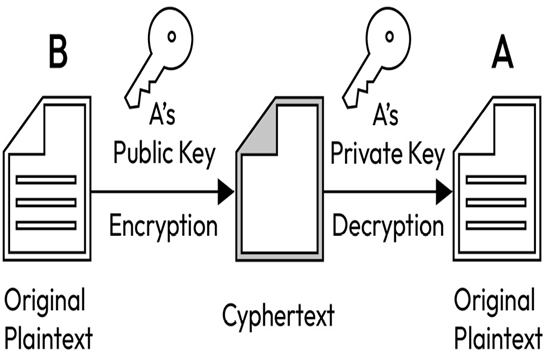
Figure 1.10 – Asymmetric encryption (http://www.giuseppeurso.eu/wp-content/uploads/2014/11/giuseppe-urso-asymmetric-key-encryption-in-java-03.png)
Let’s look at how asymmetric encryption works:
- Key generation: A user generates a key pair consisting of a public key and a corresponding private key. The public key is made openly available, while the private key is kept secret.
- Encryption: If someone wants to send a confidential message to the key pair owner, they use the recipient’s public key to encrypt the message.
- Decryption: Only the recipient who possesses the corresponding private key can decrypt the encrypted message that was sent to them using their public key.
The security of asymmetric encryption relies on the mathematical properties that make it computationally infeasible to derive the private key from the public key. As a result, the public key can be freely shared with others for encryption purposes, while the private key remains securely held by its owner for decryption. This makes asymmetric encryption a fundamental component of secure communication, digital signatures, and authentication in various applications, such as secure web browsing (HTTPS), email encryption, and digital certificates. Now that you understand the different types of encryption, let us understand another important concept: encrypting data in different stages.
