The guiding principle of DiD is the idea that a single security product will not ensure the safety of critical data. Implementing multiple security controls at distinct levels reduces the chance of breaches caused by external or internal threats. The following diagram depicts the concept of the DiD layer. This approach is designed to provide a layered defense that can stop attackers at multiple points in the attack chain, rather than having to rely on a single point of failure:
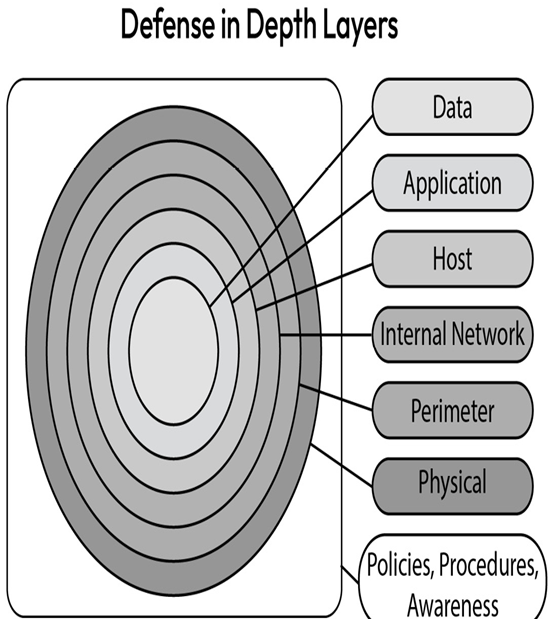
Figure 1.5 – Defense in depth (http://3.bp.blogspot.com/-YNJp1PXeV0o/UjpD7j1-31I/AAAAAAAADJE/O_6COIge7CA/s1600/TechnetDinD.jpg)
The guiding principle of DiD is a strategy that is used to provide multiple layers of protection for a system or organization. Some important security practices that are used in DiD are as follows:
- Least-privilege: Least-privilege access is the practice of granting just enough access to the user so that they can perform their designated task in the organization and restrict their access to all other resources and systems. Limiting permissions on a user’s identity helps minimize risk in case credentials are compromised and an unauthorized user attempts to access sensitive data.
- Multi-factor authentication (MFA): This is a security mechanism that requires users to provide two or more factors of authentication to access a system or application. This approach adds an extra layer of security to the authentication process, making it more difficult for attackers to gain unauthorized access. They can use either software or hardware tokens to provide an additional layer of security beyond a user’s password:
- Software tokens are typically generated by a mobile app or software program. Once the user has entered their username and password, they are prompted to enter a one-time code generated by the app or software. This code is typically valid for only a short period and changes frequently, making it difficult for attackers to intercept and reuse.
- Hardware tokens, on the other hand, are physical devices that generate one-time codes that the user must enter to complete the authentication process. These tokens may be in the form of key fobs, smart cards, or USB devices. The user inserts the hardware token into a device or presses a button to generate a code, which they then enter into the system or application being accessed.
Both software and hardware tokens provide an additional layer of security by requiring something in addition to the user’s password to gain access to a system or application. However, hardware tokens are generally considered more secure as they are not susceptible to attacks that can compromise software-based tokens, such as malware or phishing attacks. They also require physical possession of the token, making it more difficult for attackers to gain access, even if they have compromised the user’s password.
- Network segmentation: This is the practice of dividing computer networks into smaller parts to limit the exposure of internal systems and data to vendors, contractors, and other outside or inside users. This also helps the security team protect sensitive data from insider threats, limit the spread of malware, and comply with data regulations.
- Intrusion detection and prevention: Intrusion detection and prevention systems can be used to detect and prevent attacks on a system or network. These systems can be configured to alert security personnel or take automated action when an attack is detected.
- Security training: Providing security awareness training to employees is an important security practice to ensure that they understand the importance of security and are aware of common threats and attack vectors.
These are just a few examples of the security practices that are part of DiD. Implementing these practices in a comprehensive and layered approach can help improve the overall security of an organization.
